DACS One-Time Password Token Demonstration
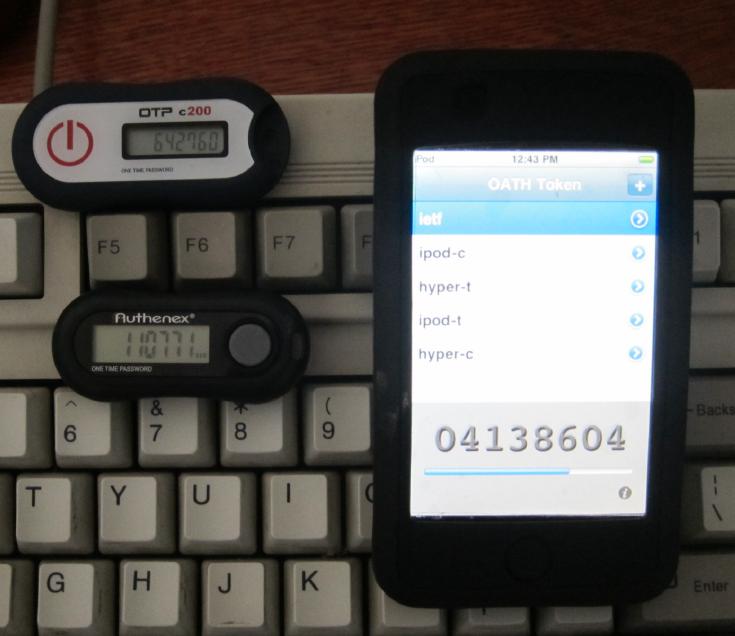
This is a demonstration of DACS
one-time password accounts using hardware or software tokens.
For background and technical information,
please refer to
dacstoken(1),
dacs_token(8), and
dacs_authenticate(8).
If you have a supported one-time password generating device
or client application, you can:
- create a demo account;
- synchronize your account with your token; and
- validate a one-time password produced by your token or application
against your account.
Note: There is a bug in 1.4.35 that breaks this demo.
If you want to try this demo on your platform,
apply
this patch
to src/auth_token.c and rebuild
DACS.
Reports of problems and suggestions for improvements are welcome -
contact us here.
Introduction
To authenticate using an OTP token, you must create
a demo account here that matches your OTP token parameters
or OTP client parameters.
While all conformant OTP tokens should provide equivalent functionality,
different client implementations have different constraints
regarding the format of the key, unfortunately.
A client may require the key to be entered as a hex number,
plaintext password, or base-32 encoded value.
If you are unable to synchronize your OTP token with your demo account,
it is most likely because the key associated with your account and the key
given to the OTP token do not match.
Some OTP software allows an account to be imported by scanning a QR Code
or following a link.
When you create a demo account here, a URL will be displayed.
If an OTP client has been registered with your browser to
handle the otpauth URL scheme and your key is in a suitable
format for the client,
clicking on the link should automatically start your client and import
the new account.
The URL is also encoded as a QR Code using the Google Charts web service
and the image is displayed.
If your OTP client is capable, or if you have a QR Code scanning app,
you can use either to import the account in the same way as the URL.
To simplify the instructions for this demo,
we will assume that you are using
Google Authenticator.
The three forms below provide operations to:
- Create a demo account,
- Synchronize a token with your demo account, and
- Validate a one-time password for your account
(authentication)
Notes:
- The username for an account is generated by the demo and
cannot be selected.
- There is a limit of one account per token type per IP address.
- If you create another account of the same type,
the older account's parameters will be replaced.
- These accounts are used only for demonstration purposes,
and all key, serial, PIN, and other demo account information is kept private
until it is periodically discarded.
[If you have installed and configured
DACS 1.4.25,
you may copy this web page and run the demo against your server.
You may need to change the action attributes in the
form elements.]
1. Create a new demo account
This form creates a new one-time password account.
If you provide a PIN, the same
PIN must be given when you submit one of
the other operations.
For your convenience,
neither the Key field nor the
PIN fields are hidden,
as they normally would be.
The Serial field is not currently used for
anything;
any unique string can be used, but if it is not provided,
a random string will be created.
Form fields marked with a * are required.
Other fields are optional.
If the operation is successful, the username for your new demo account
will be displayed.
Make a note of the username.
You will need it for the other operations.
Also shown are an XML representation of the account
(as produced by the -export flag of
dacstoken(1)),
a URL encoding of the account, and a QR Code image of the URL.
A default key in base-32 encoding ("mfrggzdf") is provided.
You may change it.
2. Synchronize your token or client with your demo account
This form is used to synchronize your token device or client application
with your demo account.
You may need to perform this operation before you can use your token
for validation or if your token stops producing correct passwords.
This can happen if the button on your HOTP token has been accidentally
pressed a few times.
For a time-based token ("TOTP mode"),
enter one password from your token in the
Sync field.
For a counter-based token,
also called an event-based token or "HOTP mode",
enter three consecutive passwords from your token,
separating the passwords with a comma.
If the account was created with a
PIN,
the same PIN must be entered here.
If the account does not have a PIN,
do not enter a PIN.
If you used the default HOTP mode parameters above and default key
("mfrggzdf"),
your synchronization passwords will be:
106998,421654,118157.
3. Validate a one-time password
To validate (check) a one-time password produced by your token or client,
enter your demo account name and a one-time password from your OTP token.
If your account has a PIN, enter it too.
No DACS credentials are actually issued.
If you are using the defaults,
the next two OTP passwords should be
"283104" and
"848242".
It will do no harm to use an incorrect password with a TOTP token,
so you can satisfy yourself that a bogus password will be rejected.
For a HOTP token, in demo mode the counter is updated only if
the given password validates correctly, so you can see what happens if you
try a password that worked previously or enter a random guess.
You can repeat the demo by creating a Time-based mode account.
Copyright (c) 2003-2015 Distributed Systems Software.
All rights reserved.
$Id: $